VWO’s privacy-first approach: what it entails, why it is essential, and how it benefits our customers.
What does privacy mean for an Experimentation Platform?
As data powers experiments, upholding the confidentiality and security of this data becomes essential. If you’re a company that runs experiments, you are governed by data privacy, security, and compliance laws applicable in your region. Therefore, it becomes essential for you to choose a privacy-first experimentation tool.
Download Free: A/B Testing Guide
The question then arises – How do you know if you can trust an experimentation platform to meet the necessary privacy-related criteria? To ascertain this, you need to evaluate what kind of data is collected by the platform, where it is stored, how it is used, and if there are any security, privacy, and compliance risks.
In this article, we’ve answered these crucial questions in the purview of VWO.
At VWO, we believe that privacy is a fundamental human right. We are committed to providing you with products, information, controls, and transparency that allow you to choose how your information, and that of your users, visitors, and customers, is processed. We owe our growth to our customers, and winning their trust is our top priority. Therefore, keeping customer data confidential and compliant is paramount to us.
Security is at the heart of how we build our products, policies, and processes to provide high resiliency. We follow security-by-design principles to protect information systems and customer information so that you can experiment and build the best customer experience using the platform you truly trust.
Which data is collected by VWO?
The entirety of the data gathered by VWO is classified into the following two categories:
- Customer Account Data: This is the customer’s data of VWO, associated with their purchase and use of the VWO Experimentation platform and services. This data includes customers’ login and contact information, campaign configurations, account configurations, billing configurations, and other similar data necessary to use and run the VWO application.
- User Data: This is the data of the visitors or end-users (who arrive at the customers’ websites/applications) collected as part of the campaigns executed via VWO. This data powers all the features in the VWO application viz session recordings, heatmaps, surveys, A/B tests, MVTs, etc.
VWO servers collect and store UUID (Unique User Identifier) information in the pseudonymized format. A UUID is a 128-bit number used to identify information in computer systems. As VWO pseudonymizes the UUID before storing it using a one-way hashing function, the information that can point to the identity of a visitor is replaced by “pseudonyms,” and the identity is protected.
VWO servers store user agent data, including the following information for customers using the report segmentation in VWO’s Experimentation Platform:
- IP Address of the visitor in an anonymized format.
- Referring URL to know from where the visitor came to your website.
- Type of visitor – new or returning.
- A location such as country, city, and region. You can select what level of location information you want to store here.
- Information on the device used to access the website, including the OS, user agent, mobile/tablet/desktop, and browser.
- Time of the visitor action or goals data includes clicks, scrolls, revenue, etc.
This data is collected as the end-user or visitor interacts with your website.
For one of our products – ‘VWO Insights’, VWO servers process additional data types for heatmaps, session recordings, surveys, and other features that provide visitor behavior insights:
- Recordings of visitors’ actions on the website to analyze visitor behavior in a video format.
- Scroll data to understand the depth of user interaction on your website content.
- Mouse movements to analyze visitor behavior on a page.
- Mutations.
- Device orientation and change behavior for mobile devices.
- HTML content of the webpage.
For lawful grounds for the processing of data, data subject rights, and purposes of processing of personal data, please refer to our privacy policy.
Where does VWO store data?
VWO has always been fully compliant with GDPR. Both VWO customers’ and their users’ data has historically been stored and processed in the US-based data center, complying with GDPR law. This data center serves over 2500 satisfied customers globally, with more than a thousand in the European Union.
We took the next natural step with a continued commitment to privacy and security. We recently launched a European Union(EU) data center to ensure that user data doesn’t leave the international EU borders. Hosted in Belgium (Europe-west1 of GCP), this data center caters to those who prefer to store and manage their end-user data within the EU. The data of the visitors as processed by VWO is as per the Data Protection Agreement (DPA) for the entities that choose to configure their accounts with this data center.

How safe is your data with VWO? Can it be leaked, distributed, or accessed?
VWO’s enterprise-grade platform has been designed keeping in mind the high level of security expected by world-class businesses. With VWO, you can rest assured that any data stored by us remains safe, confidential, and accessible. By ‘safe,’ we mean that the data will be protected against any type of loss or corruption. ‘Confidential’ means access to the data is granted only to authorized personnel, and by ‘accessible,’ we mean that the data is available only to authorized users whenever required.
This data protection guarantee comes from a combination of physical and code security, configurable application access, regular vulnerability scans, and consistent data availability. You can read more about this in our knowledge base article.
How does VWO manage data deletion and access?
By default, VWO identifies and anonymizes any Personally Identifiable Information (PII) or users’ sensitive data before storing it on its servers. PII includes passwords, social security numbers, phone, card information, and other personal data.
For deleted or expired accounts, the data is deleted within 45 to 90 days from the date of expiry. As a VWO customer, you can write to VWO support requesting immediate deletion of accounts or specific user data if you want to prioritize this.
VWO has established policies and procedures to dispose of electronic and physical media containing PII, account data, and sensitive and confidential information to ensure its servers’ data security. You can read more about it in our knowledge base article.
How is VWO’s product strategy aligned to our privacy-first approach?
At VWO, we back ourselves up with robust data security and privacy practices that form an integral part of our product engineering and development. These principles have a robust framework for building secure systems that address all threat vectors by default and by design.
Keeping in line with this, the below settings are a part of our product suite:
1. You can opt your visitors out of VWO tracking without hampering their experience on your website.
Even though VWO never tracks the end user’s personal data, your visitors have the choice to opt out of getting tracked by VWO.
As a website owner, you can make your visitors opt out of VWO by either generating an opt-out link and sharing it with your website visitors or using VWO’s opt-out API.
The opt-out API has two versions. When you fire this API in the first version, all VWO cookies are deleted, and VWO stops visitor tracking immediately. If the visitor in question returns to the page, they will still not be considered for VWO tracking. Therefore, they won’t see any campaign changes on return visits.
In the second version, you can opt a visitor out of VWO tracking but still show the experience (campaign changes) that they have seen earlier. For example, say a visitor has seen variation A of a specific campaign, and you now want to opt them out of VWO tracking while showing the same variation to the visitor on his return visits. When you fire this API, VWO stops visitor tracking immediately. However, the visitors continue to see the same variation they were previously a part of.
2. You can easily seek consent before collecting visitor data, and you can do so more responsibly than before.
In view of applicable data protection laws, it is necessary to display a cookie banner informing visitors about cookies or obtain consent before tracking their data. This ensures that you can only do so with their permission if you use tools/scripts on your website to identify individuals and their personal information.
VWO gives you the option to configure triggers for VWO Insights so that you can track visitor data more carefully, responsibly, and with consent. Any visitor action can be used to trigger the collection of Insights data. You can write custom JavaScript code that can listen for visitor actions, and decide based on the kind of pages visited or any scenario you want to validate before collecting Insights data. This knowledge base article describes the process of setting up a custom trigger in VWO.

How do we ensure cookie compliance?
VWO uses cookies and local storage to understand visitors’ behavior and track visitor journeys on your website to deliver the best experiences. The cookies identify the variation in an experiment that the visitor views and help serve the same variation to the visitor consistently. These cookies also track visitor actions, determine whether they are part of a campaign, etc. However, the only information that VWO collects about a cookie is a visitor ID, i.e., a UUID explained previously above that does not contain any personal data. This UUID helps distinguish one visitor from another, but no individual or consumer can be tracked or identified by VWO.
As part of compliance requirements under applicable data protection laws and regulations like GDPR, PECR, CCPA, etc., it is necessary to obtain informed consent from visitors before deploying any cookies or trackers to process their data. VWO does not collect any sensitive information. However, as a user, the decision to implement VWO with cookie consent or not is entirely up to you. Always consult your legal counsel to determine which implementation is appropriate for you. They can help you make an informed decision considering the data privacy rules of the countries you operate.
The VWO SmartCode is an automatically generated code snippet that you must add to enable VWO on your website. You can choose to execute the SmartCode without the visitor’s consent, i.e., you do not require any permission before deploying cookies or trackers to process visitors’ data. You can also choose to execute the SmartCode after obtaining the visitors’ consent (this is for VWO Insights and Engage; the Testing campaigns execute without the visitors’ permission). You can also go for conditional execution – here, the SmartCode is executed only after visitors’ consent is obtained, irrespective of the product you’re using. Furthermore, VWO communicates with cookie consent managers via callback when the visitor accepts or rejects the cookie, allowing you to run the SmartCode based on valid consent.
Depending on the data privacy rules in the countries you operate, you can make an informed decision. This knowledge base article discusses choosing the correct method for implementing the SmartCode.
Download Free: A/B Testing Guide
How does VWO ensure security?
More than 2500+ customers trust the VWO Experience Optimization Platform with their data, and this responsibility is something we take very seriously. All data reaching VWO servers from recordings, survey responses, or the custom dimension is encrypted using the industry-standard AES-256 encryption algorithm. You can read this knowledge base article for details.
We’ve also incorporated security fundamentals into the following aspects of our daily operations:
Organizational structure and governance
Wingify (makers of VWO) has established a Corporate Security and Compliance Team (CSC) consisting of key personnel whose responsibility is to identify security and compliance concerns across the company. This team acts as the first line of defense in enhancing the appropriate security and compliance posture. This team reports to the CEO.
Risk management – ISO

ISO/IEC 27701:2019 (ISO 27701) is internationally recognized and a global privacy standard that focuses on the collection and processing of personally identifiable information (PII). Any ISO/IEC 27701 audit requires the organization to declare applicable laws/regulations in its criteria for the audit. This means that the standard can be mapped to many of the requirements under GDPR, California Consumer Privacy Act (CCPA), and other laws. Once mapped, privacy professionals implement the ISO/IEC 27701 operational controls and audited by internal or third-party auditors, resulting in certification and comprehensive evidence of conformity.
VWO has received an accredited ISO/IEC 27701:2019 certification as a PII processor and controller after undergoing an audit by an independent third party.
ISO/IEC 27001:2022 (ISO 27001) is an internationally recognized framework that specifies the requirements for establishing, implementing, maintaining, and improving information security management within an organization. Certification standards are intended to help organizations achieve the highest level of performance possible, reduce data risk, and create an environment of continuous improvement. VWO has received the ISO 27001:2022 certification from from TÜV SÜD, internationally renowned auditing entity founded in 1866. The ISO 27001:2012 certification demonstrates our commitment to information security at every level. Compliance with this internationally-recognized standard validated by an independent third-party audit confirms that our security management program is comprehensive and follows industry-leading practices.
Access management
All users in a VWO account are assigned an access level that determines the actions users can perform in the VWO account. If you are an account owner or administrator, you can change the access level at any point in time.
Authentication and password management
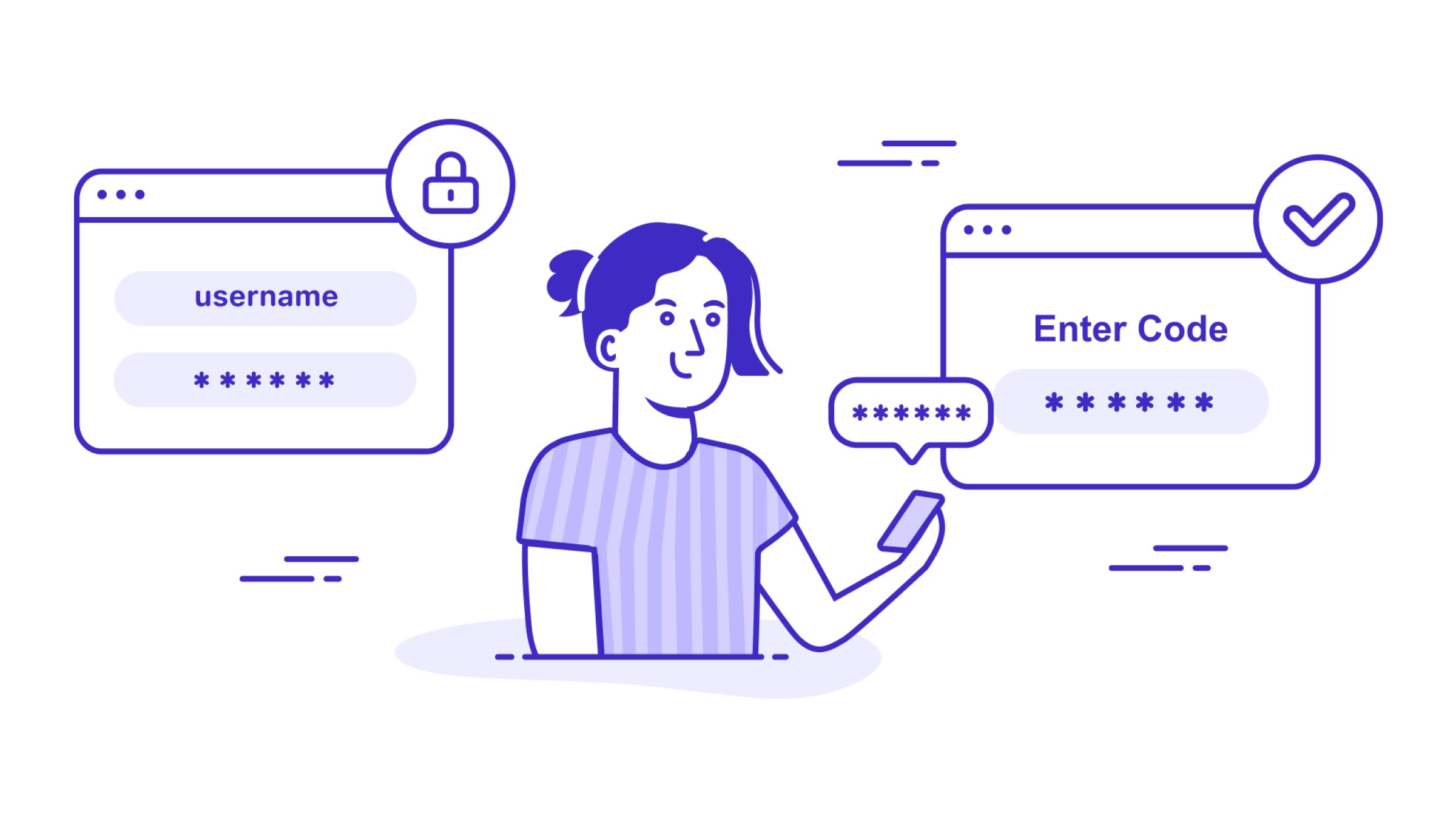
To ensure the sanctity of your VWO account, we have added an extra layer of security in the form of two-factor authentication (2FA) that prevents bad actors from accessing your data, even if they know your password.
Two-factor authentication(2FA) relies on two security measures to prevent intruders from gaining access to your VWO account. Once 2FA is enabled, to sign in to your account, you’ll need to provide something you know, i.e., your password, and something you have, i.e., a six-digit one-time code sent to your email at the login time (or by using popular TOTP based apps to generate the code).
With 2FA, you can ensure that your account is not compromised even if a malicious virus exposes your password or hackers gain access to your password by brute force.
Session management
Every time a VWO user signs in to the VWO account, the system assigns a new session identifier for the user. The session identifier is a 64-byte random generated value to protect the account against brute force attacks. After seven days, all sessions time out, requiring the users to sign in to their account again. Also, all the active sessions are set to time out after 4 hours of inactivity.
Network and transmission security
VWO is hosted on secure servers managed by GCP. Any physical access to the GCP data centers is restricted to everyone. Firewalls are configured using industry best practices, and all unnecessary ports are blocked.
As a VWO user, you are always connected to the VWO web app via HTTPS using Transport Layer Security (TLS) version 1.2 and higher, a cryptographic protocol designed to protect against eavesdropping, tampering, and message forgery.
Access control
You can assign roles and permissions to each user you add to your account to ensure an appropriate level of access to your VWO account. You can restrict access to your VWO account to specific IP addresses. You can also enable alerts to email you whenever particular activities occur in your account.
Internal access to data
The data stored on VWO’s production servers are accessible only to the SVP of Engineering and lead engineers. No other member of VWO has access to customer data unless specific access permission is granted by the Chief Executive Officer and SVP-Engineering for resolving technical issues.
Security in engineering as part of product development
Thorough quality checks are an integral part of our development process. No code goes live unless reviewed and approved by the QA team. The staging or test environment is fully separated from production and does not use any production data. Any new feature goes through a security review before being deployed to production. Also, external VAPT (Vulnerability Assessment and Penetration Testing) audits are carried out at the system level to assess for potential vulnerabilities.
Data breach
In the event of a breach in data security, we notify our customers within forty-eight hours of the incident’s detection. We have incident management policies and procedures to handle such events or emergencies.
What does all this mean for the customers of VWO?
As a customer of VWO, what this means for you in a nutshell, is as below:
- VWO collects only such data necessary for security and for the purposes of product enhancement, marketing, and analytics – and with your visitors’ consent. Any personal information, if collected, is anonymized.
- This data is stored securely and as per applicable data protection laws including GDPR, PIPEDA, CCPA, POPIA, DPDPA, etc.
- This data remains safe, confidential, and accessible to you at all times.
- Robust and safe processes govern data deletion if your account with us is deleted or expired.
- Privacy forms an integral part of our product strategy, and any product enhancements are designed on privacy-first principles.
- We ensure cookie compliance as part of data protection policies like GDPR.
- We ensure the security of your data with the help of our Corporate Security and Compliance Team by procuring and maintaining information security certification through robust access, password and session management, and relevant disaster management policies.
Our Corporate Security and Compliance Team, along with members of our senior leadership, have taken the following measures:
- We have raised awareness across the organization through frequent discussions in our internal channels and trained employees to handle data appropriately.
- We have assessed all our products individually against the requirements of the GDPR. We have implemented new features that will give you more control over your data and ease your burden of achieving GDPR compliance.
- We have appointed internal privacy trust champions for all our teams. We have also established a Data Protection Officer (DPO).
- Our application teams have embraced the concept of privacy by design and have provided you with more control over the data you store in our systems. We constantly endeavor to provide you with more enhancements, rolled out in phases. We have implemented appropriate organizational, technical, administrative, and physical safeguards to protect our organization’s security, confidentiality, integrity, and privacy of Personal Information and customer data.
With these measures in place, as a customer of VWO, you are compliant with privacy laws, your data is safe with us, and the privacy of your website visitors is respected and protected at all times.
As an experiment owner not using VWO, it is not sufficient if you’re simply privacy-conscious. You will need to prioritize data privacy and integrate it within your experimentation stack as well as your roadmap. You can get in touch with our product experts if you wish to understand more about how VWO can help you do so.
Frequently Asked Questions (FAQs)
Common data privacy concerns with A/B testing tools usually revolve around how user data is collected, stored, and processed. Some key concerns include:
– Personal data collection: Experiments may capture identifiable information if tracking is not properly configured.
– User consent and cookies: Many testing tools rely on cookies or similar technologies, which require transparent consent mechanisms.
– Data storage and transfers: Where data is stored and whether it crosses regional boundaries can raise compliance issues.
– Third-party integrations: Connecting testing tools with analytics, CRM, or marketing platforms can increase data exposure if not managed carefully.
– Anonymization and security: Ensuring data is pseudonymized, encrypted, and accessed only by authorized teams is critical.
To address these concerns, teams should opt for privacy-focused tools like VWO that implement clear consent flows and follow secure data governance practices.